Search here to choose from a wide range of courses and programmes offered in our nation-wide campuses

JUGNU UBEROI
Industrialist
Christ University
Bachelor of Commerce (BCom)
1972

Ravi S
Indian Police Service
Christ University
PCMB (Christ College)
1996

P N Krishna Kumar
Wing Commander
Indian Armed Forces
Christ University
Bachelor of Commerce (BCom)
1993

B G Jagadeesh
Brigadier
Indian Armed Forces
Christ University
BSc PCM
1983

Syed Asad Abbas
National Television Media Personality
Christ University
MS Communication
2011

HARESH THARANI
Bachelor of Commerce (BCom)
(1982)
Chairman & CEO
Tharanco Group

NUPUR RASHI PANNA
BSc CME
(2006)
IAS
Indian Administrative Service

ABDULLAH RASHEED
Bachelor of Education
(2011)
Principal
Huravee School
Ministry of Education Republic of Maldives
VISWAKUMAR MENON
BA JPEnglish
(1995)
Associate Director Global Head of PR & Media Relations
Tata Communications

KURUVILLA CHERIAN
Bachelor of Commerce (BCom)
(2005)
Executive Director
EY

YATEESH BEGOORE
Legal Officer
Organisation for the Prohibition of Chemical Weapons (OPCW)
The Hague

GAUTHAM KARTHIK
BA Communication and Media, English and Psychology (CEP)
(2012)
Indian Actor
Film Industry

ANDREW CHAKRABORTY
Lawyer
Bradley Allen Love Lawyers, Canberra, Australia

AVINASH KAPOLI
Bachelor of Hotel Management (2004-08)
Trade Ambassador
Bacardi India Pvt. Ltd.

SUDHIR UNNIKRISHNAN
Bachelor of Commerce (BCom)
(1989)
SVP and Managing Director (India)
Blume Global

MALLIKHARJUNA RVR
Department of Computer Science MCA
(2001)
Head Of Mobile Technology
Axis Bank

SHWETA SASTRI
Bachelor of Business Management (BBM)
(2004)
Managing Director
Canadian International School Bangalore

MADONNA SEBASTIAN
Bachelor of Commerce Tourism
(2013)
Indian Actress
Tamil/Malayalam

BRUCE LEE MANI
BA JPEnglish
(1998)
Musician
Director, Taaqademy

SANJAY SHAND
Bachelor of Commerce (BCom)
(1989)
Managing Director
Shand Group of Industries

AJITH NAYAR
Bachelor of Hotel Management (1992 - 95)
Co Founder & CMO,
Camcom

BABU C JOSEPH
BSc PCM
(1987)
Chairman and Managing Director
White Group
KRISHNA BYRE GOWDA
Bachelor of Business Management (BBM)
(1994)
Politician
MLA, Byatarayanapura Constituency, Bangalore

BHUVAN G M
Bachelor of Hotel Management (1991 - 94)
Professor & Principal,
Apeejay Institute of Hospitality, Navi Mumbai

SRUTHI HARIHARAN
Bachelor of Business Management (BBM)
(2009)
Indian Actress / Producer (Kannada)
Film Industry

SAMYUKTA HORNAD
BA Communication and Media, English and Psychology (CEP)
(2012)
Indian Actress / Model (Kannada)
Film Industry

YOGESH BHAT
Bachelor of Business Management (BBM)
(1995)
Senior Vice President
Masai School

GAURAV SAIT
Master in Business Administration (MBA)
(2008)
Vice President
JP Morgan
_20230321123703..png)
AMULYA K G
Bachelor of Business Management (BBM)
(2009)
Indian Defence Accounts Service
Deputy Controller Defence Accounts, MEG (Madras Engineering Group) & Centre Bangalore

NIRANJAN NARAYANASWAMY
BA JPEnglish
(2007)
Executive Editor - News
Republic TV

DHANYA SKARIACHAN
BA JPEnglish
(2006)
Business Editor
Deccan Herald

MOHAMMED ZAHRIN BIN AZIZ
Bachelor of Hotel Management (BHM)
(2014)
Restauranteur
Director, Empire Group of Restaurants

PARINIKA PAVAN RAM
Bachelor of Commerce (BCom)
(2016)
KAS
Karnataka Administratice Service (KAS)

RAJEEV RAVINDRANATHAN
Bachelor of Business Management (BBM)
(1997)
Indian Actor
Film Industry

KETAN PISHE
Bachelor of Business Management (BBM)
(2001)
Partner
P N RAO FINE SUITS

GEORGE POTHAN POOTHICOTE
Bachelor of Commerce (BCom)
(2007)
Advocate, Supreme Court of India
Legal Consultant, Ministry of External Affairs

JOSE THOMAS
Bachelor of Hotel Management (BHM)
(1999)
Exective Chef
Taj Hotels Resorts and Palaces

MADHUKESHWAR DESAI
BA LLB
(2011)
Politician and Lawyer
National Vice President, Bharatiya Janata Yuva Morcha

SHILPI NEHA TIRKEY
Bachelor of Business Administrtaion (BBA)
(2010)
Politician
Member of Legislative Assembly Mandar Constituency

CHAITANYA K M
BA Communication and Media, English and Psychology (CEP)
(1994)
Film Director
Documentary Maker and Theater Person

SHILPA NAG
Master of Business Administration (MBA)
(2009)
IAS
Indian Administrative Service

LUCAS THOMAS
Master of Computer Applications (MCA)
(2000)
Senior Vice President
Bank of America

JOEL T V
BCom
(2011)
Vice President
Goldman Sachs

SAMI FAIZULLAH
BCom
(2014)
Senior Vice President
Bank of America

FOUZIA TARANUM
PGDM
Indian Administrative Service (IAS)

K FRANCIS GEORGE
Politican
Ex-Member of Parliament,
Lok Sabha

M N REDDI
Indian Police Service (IPS)
Former Commissioner of Police
Bangalore City

C B RISHYANTH
BCom
Indian Police Service (IPS)

SRIRAM SULIA
(2009)
Radio Jockey
Head of Programming
FEVER FM & RADIO ONE

PUNEET KOTHAPA
BCom
President
The Narayana Group
_20230321044343..png)
SUPRIYA LOHITH
BSc CMS
(2006)
Playback Singer
South Indian Films

SRINATH SATHYANARAYANA
MCA
(1999)
Chief Technology Officer
Fincare

TRISHIKA KUMARI WADIYAR
MA Economics
Maharani of Mysore and
Wife of Yaduveer Krishnadatta Chamaraja Wadiyar
27th Maharaja (King) of Mysore

MADAN KUMAR
MCA
(2004)
Managing Director
Accenture's Advanced Technology Centers in India

NEHA CADABAM
MSc Psychology
(2010)
Psychologist
Executive Director
Cadabams Group

KARAN MACHADO
BA CEP
(2014)
Radio Jockey
94.3 Radio One

MONICA JAIN
BA Economics Honours
(2016)
Climate Change Consultant
The World Bank

POOJA CHHABRIA
BA CEP
(2012)
Digital Editor
World Economic Forum

RUBEN RAJAMANICKAM
(2001)
Senior Vice President
JP Morgan Chase & Co

KALMESHWAR SHINGENAVAR
MBA
(2006)
Indian Police Service (IPS)

PRADEEP JOHN
BA HEP
(1999)
Second in Command
Central Reserve Police Force
Chennai

ANIRUDH R GANGAVARAM
BBA
(2018)
Indian Revenue Service

CHOCKO VALLIAPPA
BCom
(1988)
CEO, Vee Technologies
Vice Chairman, Sona Group of Instituions

ANTHONY HUANG
BHM
Executive Chef
Sheraton Grand Bangalore

NEHA CADABAM
BA (Psychology, Communicative English, Literature)
MSc Clinical Psychology
2005 - 2010
Executive Director, Cadabams Group
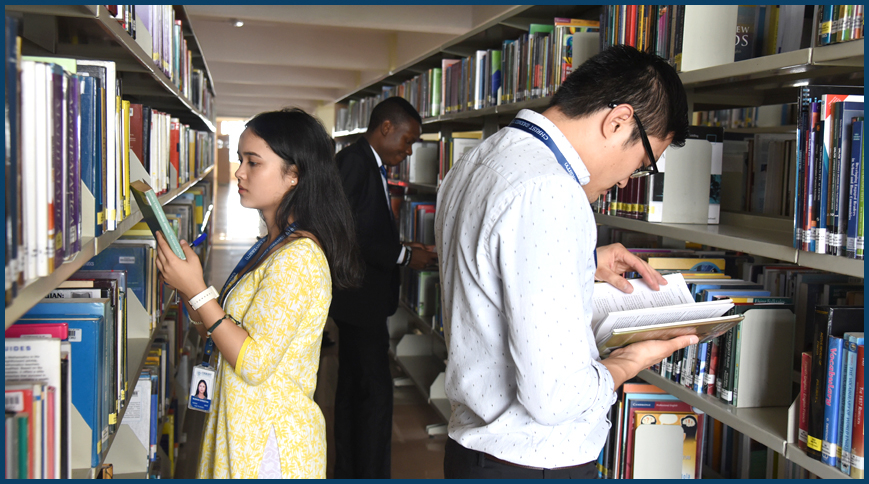
A well-equipped infrastructure to promote the academic and cultural activities of CHRIST is one of our primary accomplishments. An attempt to provide equal opportunity for each and every Christite is the idea behind this unique feature of our campus.











Countries
Academic Departments
International Students
Library Books
Alumni
Dharmaram College Post, Hosur Road, Bengaluru - 560029,
Karnataka, India
Tel: +91 804012 9100 / 9600
Fax: 40129000
Email: mail@christuniversity.in
Web: http://www. christuniversity.in
EXCELLENCE AND SERVICE
CHRIST (Deemed to be University) is a nurturing ground for an individual's holistic development to make effective contribution to the society in a dynamic environment.